Forging Trust in the Face of Cyber Threats
In today’s hyperconnected world,
trust is the cornerstone of the digital economy. Every transaction,
communication, and exchange of information relies on it. Yet, with the rapid
rise of cyber threats, trust has become increasingly fragile. Cyberattacks like
ransomware, phishing, and data breaches are eroding confidence in the safety of
online environments. For businesses, governments, and individuals, the
challenge is to find ways to safeguard this trust while navigating an
ever-changing threat landscape.
In this article, we will dive
deep into the nature of cyber threats, explore how trust is affected by
breaches in security, and examine actionable strategies for forging and
maintaining trust in the digital era.
Understanding the Cyber Threat Landscape
Types of Cyber Threats: A Breakdown:
Cyber threats come in many forms, each designed to exploit
vulnerabilities in digital systems and human behaviors. The most prominent
types include:
Ø Phishing and Social Engineering: Phishing remains one of the most prevalent and successful forms of attack, primarily due to its reliance on human error. Phishing emails and fake websites deceive users into divulging sensitive information such as passwords, credit card numbers, or login credentials. Social engineering tactics manipulate individuals into compromising their security by posing as trusted entities, amplifying the success rate of these attacks.
Ø
Ransomware:
Ransomware attacks have become more common and damaging. In this form of
attack, hackers infiltrate systems, encrypt critical data, and demand a ransom
to restore access. Recent incidents like the Colonial Pipeline ransomware
attack in the U.S. highlight the devastating impact these threats can have on
infrastructure and business operations.
Ø
Data
Breaches: Data breaches involve unauthorized access to systems containing
sensitive data. Attackers typically aim to steal valuable information—such as
customer details, financial records, or intellectual property—that can be sold
on the dark web or used for identity theft. High-profile breaches like the one
experienced by Equifax in 2017 exposed the data of millions of people, severely
damaging the company’s reputation and leading to costly legal repercussions.
Ø
Insider
Threats: Not all threats come from external actors. Insider threats involve
employees or contractors who misuse their access to sensitive information,
either intentionally or unintentionally. According to a 2021 Verizon Data
Breach Investigations Report, insider threats accounted for 22% of all security
incidents, making it a significant risk factor.
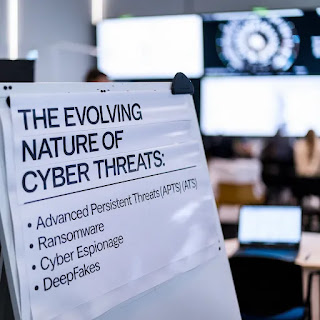
The Evolving Nature of Cyber Threats:
The cyber threat landscape is constantly evolving. Attackers are becoming more innovative, employing advanced techniques such as AI-driven attacks, polymorphic malware (which constantly changes its code to evade detection), and deepfake technology. Furthermore, the rise of nation-state-sponsored cyberattacks has blurred the lines between cybercrime and cyberwarfare, making the threat landscape even more complex and dangerous.
Impact on Digital Trust:
Each new cyberattack—especially
high-profile breaches—has a significant, often long-lasting impact on digital
trust. When customers hear about security breaches involving their personal
data, they are likely to lose faith not only in the affected company but also
in the security of digital services in general. This erosion of trust affects
all parties in the digital ecosystem: businesses, governments, and individuals.
Ø
Business
Consequences: Companies that suffer from data breaches can experience a
sharp decline in customer loyalty, as well as financial losses. For instance,
following the Target breach in 2013, where the personal data of 40 million
customers was stolen, the company faced severe reputational damage and over
$162 million in legal and settlement costs.
Ø
Government
Impact: For governments, a breach of trust can have far-reaching
consequences. Cyberattacks targeting critical infrastructure (e.g., power
grids, healthcare systems) can shake citizens’ confidence in their government’s
ability to protect them. This was evident during the 2020 SolarWinds
cyberattack, which exposed vulnerabilities in U.S. government agencies and
corporate systems.
The Importance of Trust in Cybersecurity
Digital Trust: The Foundation of Online
Transactions:
Digital trust is the foundation upon which the modern internet operates. From e-commerce transactions and online banking to telemedicine and cloud-based business applications, secure data exchanges are vital. Trust underpins every aspect of digital life, but trust is fragile. A single breach can destroy years of customer confidence, leading to massive financial losses and legal penalties.
Trust Between Businesses and Consumers:
Customers are increasingly aware
of the risks associated with sharing personal data online. As a result, they
expect businesses to prioritize cybersecurity and protect their personal
information. According to a survey by IBM Security in 2020, 78% of consumers say
that a company’s ability to keep their data safe is the most important factor
in maintaining trust.
Companies must invest in
cybersecurity not just for compliance but to foster long-term trust. Brands
like Apple have earned a reputation for putting privacy and security first,
which helps maintain a loyal customer base. By contrast, businesses that suffer
from repeated security incidents often lose customer trust, as seen with
Yahoo’s multiple data breaches, which led to the loss of millions of users.
Government and Citizen Trust:
In the context of governments, cybersecurity plays an essential role in maintaining public trust. Citizens expect that their government can protect essential services and sensitive information, including medical records, social security numbers, and voting data. Any failure to do so can lead to societal instability, increased political scrutiny, and citizen unrest.
Governments around the world have
started to increase investments in cybersecurity infrastructure and data
protection laws. In the European Union, the General Data Protection Regulation
(GDPR) requires that organizations take extensive measures to protect user data
or face hefty fines. This regulatory framework has set a new global standard
for data protection and consumer trust.
Technology Dependence: Trust and Risk
Our growing dependence on digital
technologies further increases the need for robust cybersecurity frameworks.
With the rise of cloud computing, remote work, e-commerce, and IoT (Internet of
Things) devices, the amount of sensitive data being shared over networks has
multiplied. Each of these innovations provides immense benefits but also opens
up new vulnerabilities that cybercriminals are eager to exploit.
Without continuous improvements
in cybersecurity, trust in these technologies—and by extension, in digital
society itself—can erode rapidly.
Challenges in Forging Trust
Lack of Transparency:
One of the most significant challenges businesses face in building trust is the lack of transparency around cybersecurity practices. Customers rarely know what measures are in place to protect their data, and when breaches occur, companies are often slow to inform users. According to research by TrustArc, 79% of businesses delay reporting breaches until absolutely necessary, typically because they fear reputational damage. However, this lack of openness can cause greater harm in the long run.
Regulatory Challenges Across Borders:
The fragmented nature of global
cybersecurity regulations presents another challenge. While some regions, such
as the European Union with GDPR, enforce strict data protection laws, others
have far weaker regulations. Companies operating globally must navigate this
complex landscape and ensure compliance with different standards. This can
create inconsistencies in security measures and a lack of uniformity in
trust-building across jurisdictions.
Balancing Security and Usability:
In the pursuit of security,
companies sometimes make user experiences unnecessarily difficult. Strong
security practices such as multi-factor authentication (MFA), complex
passwords, and frequent system updates can create friction for users, leading
to dissatisfaction or avoidance of these systems altogether. This friction is
particularly evident in the financial sector, where customers often feel
overwhelmed by complex security protocols.
The key is to balance strong
security with a seamless user experience. Companies that make it easier for
customers to stay secure without sacrificing convenience will fare better in
maintaining trust.
Legacy Systems and Technical Debt:
Legacy systems, particularly in
industries like healthcare, finance, and government, pose a significant
challenge to maintaining trust. Many organizations rely on outdated software
and hardware, which may lack modern security features. These systems are highly
vulnerable to attacks and can result in catastrophic breaches if not properly
upgraded. Technical debt—the backlog of outdated technology in need of modernization—poses
an ongoing risk to cybersecurity and trust.
Key Strategies for Forging Trust
1. Proactive Cybersecurity Measures:
The most effective way to build
trust is by taking a proactive approach to cybersecurity. Businesses must
implement best practices such as:
Ø
End-to-End
Encryption: Ensuring that all data exchanged between systems and users is
encrypted to prevent interception by malicious actors.
Ø Security Updates and Patching: Regularly updating software and systems to patch known vulnerabilities is critical. Many breaches occur because attackers exploit outdated software.
Ø
Multi-Factor
Authentication (MFA): By requiring two or more verification steps,
businesses can significantly reduce the risk of unauthorized access.
Ø
Regular
Security Audits: Conducting frequent audits helps identify weaknesses in
systems, networks, and procedures before they can be exploited.
2. Cultivating a Culture of Security:
Building a culture of security
within organizations is critical. Employees must understand the importance of
cybersecurity and their role in protecting company assets. This can be achieved
through:
Cybersecurity
Training: Regular training sessions on identifying phishing attempts,
creating secure passwords, and handling sensitive data.
Simulated Cyber
Attacks: Phishing simulations and other controlled tests to raise awareness
and prepare staff for potential threats.
3. Transparency and Communication:
Transparency is key to fostering
trust. Companies should clearly communicate their cybersecurity practices to
customers and be transparent when breaches occur. Breach notification laws—like
those in the EU and U.S.—mandate that companies inform affected individuals
within a specific timeframe. However, going beyond legal requirements and maintaining
an open dialogue with customers builds trust.
4. Adhering to Global Cybersecurity Standards:
Adopting recognized cybersecurity
standards and frameworks, such as ISO/IEC 27001, NIST (National Institute of
Standards and Technology), and GDPR, ensures that businesses are following best
practices for data protection and risk management. This helps standardize
security measures across different regions and industries, increasing trust
among global customers.
5. Leveraging AI and Machine Learning in Cybersecurity:
The rise of artificial
intelligence (AI) and machine learning has transformed how organizations can
respond to cyber threats. AI-powered systems can detect patterns and anomalies
in vast amounts of data much faster than humans, helping to identify and
mitigate potential attacks before they cause damage. Automation in
cybersecurity can provide real-time responses to threats, reducing response
times and minimizing the impact of incidents.
The Role of Trust in Emerging Technologies
Blockchain: A Trustworthy Framework
Blockchain technology has emerged
as one of the most trustworthy frameworks for securing transactions. Its
decentralized, immutable ledger ensures that all transactions are transparent
and tamper-proof, making it particularly attractive in industries such as
finance, healthcare, and supply chain management. Companies leveraging
blockchain can provide customers with an added layer of trust.
Zero Trust Architecture
The Zero Trust security model is
gaining momentum as an effective way to manage access to sensitive systems.
Rather than assuming that users within a corporate network are trustworthy,
Zero Trust operates on the principle of "never trust, always verify."
Each access request must be verified and authenticated, reducing the risk of insider
threats and external breaches.
Securing IoT Ecosystems
With the proliferation of
Internet of Things (IoT) devices—smartphones, wearables, home appliances, and
industrial sensors—security risks have expanded. IoT devices often lack robust
security features, making them vulnerable to exploitation. To build trust in
IoT, businesses must implement strong encryption, secure device firmware, and
regular updates to ensure that every connected device remains secure.
Case Studies: Success and Failures in Building
Trust
Microsoft: Leading the Way in Cybersecurity
Microsoft has long been a leader
in cybersecurity innovation. By investing heavily in AI-driven security
solutions, frequent software updates, and global threat intelligence networks,
the company has maintained trust even as cyber threats have escalated. Their
cloud security services, such as Azure Security Center, have set a benchmark
for protecting enterprise systems.
Equifax: A Breach of Trust
In contrast, Equifax’s 2017 data
breach serves as a cautionary tale. The breach, which exposed the personal
information of 147 million people, was caused by failure to patch a known
vulnerability. The company’s delayed response and poor communication compounded
the issue, resulting in a massive loss of consumer trust, legal penalties, and
ongoing reputational damage.
Conclusion: Safeguarding Trust in a Digital World
In the face of ever-growing cyber
threats, building and maintaining trust is not just a priority—it’s a
necessity. Trust is the currency of the digital age, and organizations that
fail to protect it risk losing everything. By taking a proactive approach to
cybersecurity, being transparent with users, and adopting cutting-edge
technologies, businesses can navigate the evolving threat landscape while
preserving the trust that drives their digital success.
Is your organization doing everything it can to protect the digital trust of your customers?